Documentation Index
Fetch the complete documentation index at: https://docs-dev.auth0-mintlify.app/llms.txt
Use this file to discover all available pages before exploring further.
Configure ORTs
Online Refresh Tokens (ORTs) must be enabled at the API (Resource Server) level using the Auth0 Dashboard or the Management API.Configure using the Dashboard
- Navigate to Dashboard > Applications > API.
- Select the API you want to configure.
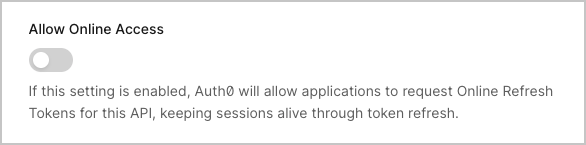
-
In the Settings tab, enable the Allow Online Access toggle.
- Select Save.
Configure using the Management API
To enable ORTs, make aPATCH call to the Update Resource Server endpoint:
GET call to the resource server:
allow_online_access property:
Get an ORT
To get an ORT, include theonline_access scope in your authorization request using the Authorization Code Flow or Authorization Code Flow with PKCE.
ORTs are prefixed with
ORT to distinguish them from refresh tokens. However, you should treat the token as opaque and not rely on its internal structure.Use an ORT
Exchange the ORT for a new access token when the current access token expires or is about to expire:openid scope, the response includes a new ID token:
Auth0 does not issue a new
refresh_token and as ORTs do not rotate, you continue using the same ORT for subsequent exchanges.Session extension behavior
Each successful token exchange:- Resets the session idle timeout: The idle timeout is restored to its full duration.
- Does not extend absolute lifetime: The session’s absolute expiration remains unchanged.
- Maintains SSO: Other applications can get tokens via SSO as long as the session is alive.
Revoke an ORT
When you revoke an ORT, it terminates the entire Auth0 session, not just the token. This invalidates all ORTs bound to that session and ends SSO for the user.Use ORTs with Actions
You can use ORTs with Auth0 Actions and the post-login trigger. Using Actions you can:- Use the
event.refresh_tokenobject to determine if the token is an ORT. - Access session specific data using the
event.sessionobject to make decisions based on the current session state
Auth0 revokes the entire user session rather than just the token, when the
api.refreshToken.revoke() method is used with an ORT.
